In October 2023, a significant software security vulnerability was discovered that impacts Microsoft Teams. The vulnerability, designated as CVE-2023-4863, affects not only Microsoft Teams but also Microsoft Edge, Skype for Desktop, and WebP Image Extensions.
Although software updates have been released for Microsoft Teams, Microsoft Defender continues to flag multiple devices as vulnerable. The persistence of this vulnerability is due to the Machine-wide Installer, which installs Teams for all profiles, while deployed updates only update the Teams.exe file for the logged-in user.
While Microsoft does not provide direct remediation for this specific issue, there are steps you can take to address it. Although manual remediation via scripting may not be ideal, a script released on GitHub by Lee Vilenski has proven to be very successful.
We have modified Vilenski’s script to meet our requirements and deployment methods, as shown below. The original script can be found here.
# Define minimum acceptable version (replace with your desired version)
$minVersion = “1.7.00.8651”
############### Do Not Edit Below This Line #################################
###Finding SIDs for loop
# Regex pattern for SIDs
$PatternSID = ‘S-1-5-21-\d+-\d+\-\d+\-\d+$’
# Get Username, SID, and location of ntuser.dat for all users
$ProfileList = gp ‘HKLM:\SOFTWARE\Microsoft\Windows NT\CurrentVersion\ProfileList\*’ | Where-Object {$_.PSChildName -match $PatternSID} |
Select @{name=”SID”;expression={$_.PSChildName}},
@{name=”UserHive”;expression={“$($_.ProfileImagePath)\ntuser.dat”}},
@{name=”Username”;expression={$_.ProfileImagePath -replace ‘^(.*[\\\/])’, ”}}
# Get all user SIDs found in HKEY_USERS (ntuder.dat files that are loaded)
$LoadedHives = gci Registry::HKEY_USERS | ? {$_.PSChildname -match $PatternSID} | Select @{name=”SID”;expression={$_.PSChildName}}
# Get all users that are not currently logged
$UnloadedHives = Compare-Object $ProfileList.SID $LoadedHives.SID | Select @{name=”SID”;expression={$_.InputObject}}, UserHive, Username
# Loop through each profile on the machine
Foreach ($item in $ProfileList) {
# Load User ntuser.dat if it’s not already loaded
IF ($item.SID -in $UnloadedHives.SID) {
reg load HKU\$($Item.SID) $($Item.UserHive) | Out-Null
}
#####################################################################
# Check and potentially remove outdated Teams versions
# Get Teams uninstall keys for the user
$teamsUninstallKeys = Get-ItemProperty registry::HKEY_USERS\$($item.SID)\Software\Microsoft\Windows\CurrentVersion\Uninstall\Teams*
if ($teamsUninstallKeys) {
foreach ($teamsKey in $teamsUninstallKeys) {
# Check DisplayVersion and remove key if outdated (with confirmation)
$displayVersion = $teamsKey.DisplayVersion
if ($displayVersion -lt $minVersion) {
$uninstallString = “C:\Users\$($item.Username)\appdata\local\microsoft\teams\update”
# Consider error handling for uninstall process (not shown here)
try {
Start-Process -FilePath $uninstallString -ArgumentList “–uninstall” -Wait -Verb RunAsAdministrator
} catch {
}
# Remove the Teams uninstall key (use with caution)
Remove-Item -Path “registry::HKEY_USERS\$($item.SID)\Software\Microsoft\Windows\CurrentVersion\Uninstall\$($teamsKey.PSName)” -Recurse}
}
} # Unload ntuser.dat
IF ($item.SID -in $UnloadedHives.SID) {
[gc]::Collect()
reg unload HKU\$($item.SID) | Out-Null
}
}
################## Remove Teams where Regkey doesn’t exist #############################
$userProfiles = Get-ChildItem -Path “C:\Users” -Directory -Exclude Default,Public
# Loop through each user profile
foreach ($profile in $userProfiles) {
# Check if Teams executable exists
$teamsPath = Join-Path -Path $profile.FullName -ChildPath “AppData\Local\Microsoft\Teams\current\Teams.exe”
if (Test-Path $teamsPath) {
# Get the installed version
$installedVersion = (Get-ItemProperty $teamsPath).VersionInfo.FileVersion
# Check version – inform about outdated and above versions
if ($installedVersion -lt $minVersion) {
Write-Host “Outdated Teams version found in $($profile): $installedVersion”
# Uninstall Teams (requires admin privileges)
Remove-Item -Path $teamsPath -Recurse -Force -ErrorAction SilentlyContinue
if ($?) {
Write-Host “Uninstalled Teams from $profile successfully.”
} else {
Write-Host “Failed to uninstall Teams from $profile.”
}
} else {
Write-Host “Teams version in $profile ($installedVersion) is above or meets the minimum requirement.”
}
}
}
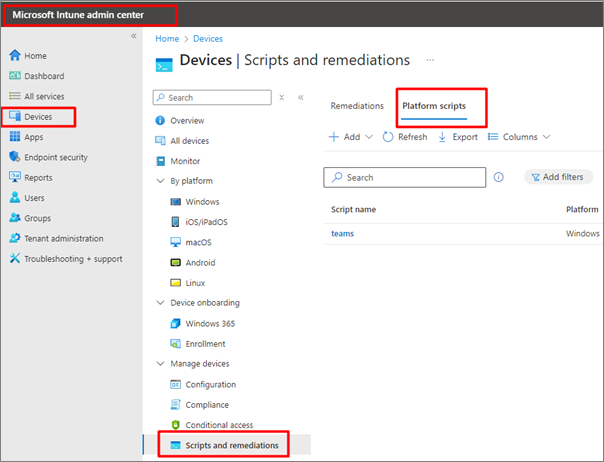
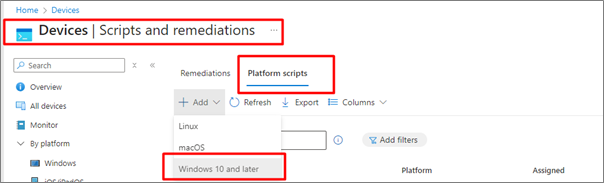
3. Select Add/Create to create a new script, select Windows 10 and later
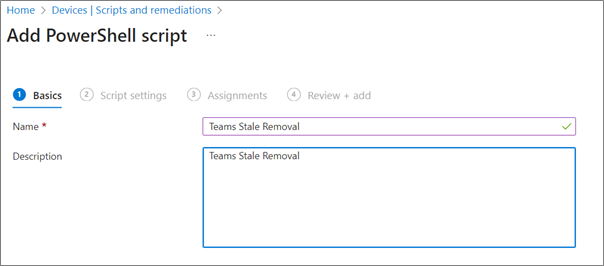
4. Enter Name and Description for script
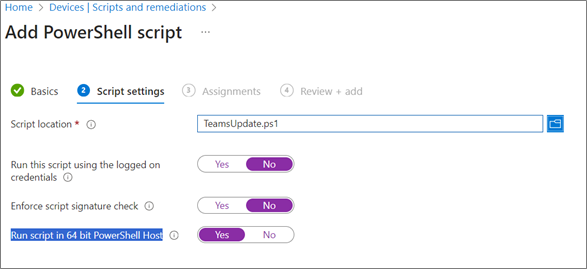
5. Under script settings:
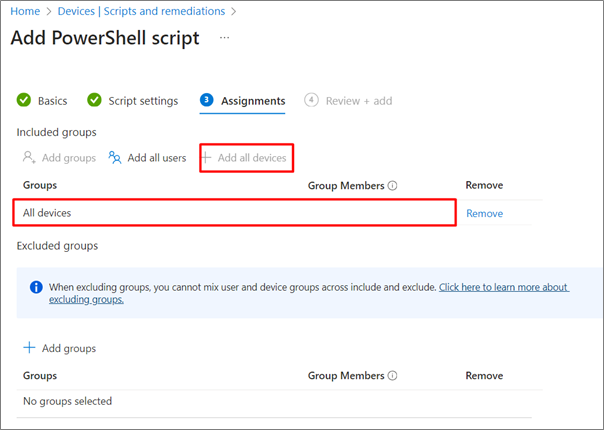
6. On next screen, Assign the script to the All devices group
7. Save
By BUI SecOps Principal Technical Consultant, Terryanne du Toit and BUI SecOps Technical Consultant, Danie Miller.
By Neil du Plessis | Cloud Security Architect, BUI
The artificial intelligence that powers Copilot for Microsoft 365 is also used in neighbouring Microsoft technologies for the modern workplace. Copilot for Azure, Copilot for Sales, Copilot for Service, Microsoft Copilot Studio, and Microsoft Copilot for Security are either coming soon or already available to Business and Enterprise customers. Let’s take a closer look at each one.
Microsoft describes Copilot for Azure as an AI-powered assistant that simplifies the design, operation, optimisation, and troubleshooting of applications and infrastructure within the Azure ecosystem. It utilises Large Language Models, the Azure control plane, and insights about your Azure and Azure Arc-enabled assets to help you streamline cloud orchestration and management.
Highlights: Copilot for Azure can help you design and develop your cloud applications, choose the best frameworks, languages, and tools, and test and debug your code. It can also help you deploy and manage your applications by providing automation, scalability, and monitoring. In addition, Copilot for Azure can recommend ways to optimise costs and improve security and compliance in your environment.
Availability: Copilot for Azure is currently in preview, and existing Azure customers and Microsoft Partners can apply to participate. If you’re interested, review the registration process before filling in the application form.
Copilot for Sales is designed to help your sales teams boost productivity, improve customer engagements, and close more deals. It takes the foundational capabilities of Copilot for Microsoft 365 and enhances them by connecting to customer relationship management platforms (like Microsoft Dynamics 365 Sales and Salesforce Sales Cloud) and providing sales teams with relevant in-app insights and recommendations to enhance customer interactions.
Highlights: According to Microsoft, Copilot for Sales empowers your sellers to simplify daily tasks, personalise customer interactions, and streamline workflows. From drafting emails in Outlook and setting up meetings in Teams to creating pitch decks in PowerPoint and data visualisations in Excel, Copilot for Sales is geared to help sales teams accomplish more in less time with AI-powered communication, content, and CRM activities.
Availability: Copilot for Sales is available now for $50 per user per month, which includes the requisite Copilot for Microsoft 365 licence. If you already have Copilot for Microsoft 365 (via your Office 365 E3, Office 365 E5, Microsoft 365 E3, Microsoft 365 E5, Microsoft 365 Business Standard, or Microsoft 365 Business Premium subscription), then you can get Copilot for Sales for an additional $20 per user per month. The Copilot for Sales pricing guide has further details, terms, and conditions.
Copilot for Service applies artificial intelligence to your call centre operations to help your customer service and support teams handle customer interactions more efficiently. Copilot for Service brings together all relevant content from your CRM platforms, websites, SharePoint sites, and third-party knowledge bases (like Salesforce, ServiceNow, and Zendesk) and puts it at your agents’ fingertips through conversational AI.
Highlights: Your customer service and support teams can enter natural language prompts and Copilot for Service will generate answers based on your organisational content – from call centre playbooks and user manuals to customer records and case histories in your CRM tools. Your agents can do this in their flow of work during real-time engagements with customers to handle queries faster, resolve issues earlier, and improve customer satisfaction over time.
Availability: Copilot for Service is available now for $50 per user per month, which includes the requisite Copilot for Microsoft 365 licence. If you already have Copilot for Microsoft 365 (via your Office 365 E3, Office 365 E5, Microsoft 365 E3, Microsoft 365 E5, Microsoft 365 Business Standard, or Microsoft 365 Business Premium subscription), then you can get Copilot for Service for an additional $20 per user per month. The Copilot for Service pricing guide has further details, terms, and conditions.
Unveiled by Microsoft at the 2023 Microsoft Ignite conference, Microsoft Copilot Studio is a low-code tool that enables you to tailor Copilot for Microsoft 365 and build your own AI-driven copilots by leveraging conversational features like custom GPTs and generative AI plugins.
Highlights: With Microsoft Copilot Studio, you’re able to personalise Copilot for Microsoft 365 according to your business needs. You can develop, test, and publish standalone copilots and regulate and secure them with the appropriate permissions, data access, and user controls. You can also see the end-to-end lifecycle of your customisations and standalone copilots in one place, which makes building, deploying, managing, and analysing them easier and simpler. In addition, you can use Microsoft Copilot Studio to link Copilot to other data sources to access any system of record, including SAP, ServiceNow, and Workday.
Availability: Microsoft Copilot Studio is available now, and the integration with Copilot for Microsoft 365 is currently in public preview. The Microsoft Copilot Studio website has further details, terms, and conditions.
Microsoft Copilot for Security was also announced at the 2023 Microsoft Ignite conference, where Microsoft explained it as an AI-powered cybersecurity product that “enables security professionals to respond to cyberthreats quickly, process signals at machine speed, and assess risk exposure in minutes”.
Highlights: Microsoft Copilot for Security combines an advanced Large Language Model with a security-specific model informed by Microsoft’s unique global threat intelligence and more than 65 trillion daily signals. The result is a sophisticated, security-focused AI assistant that can provide actionable responses to your natural language questions. These responses can be in the form of text, code, or a visual that helps you understand the full context of a security incident, its impact, and the next steps you should take for remediation and defence hardening.
Availability: Microsoft Copilot for Security is currently in private preview through an invitation-only Early Access Programme for customers and Microsoft Partners. BUI is participating in the Microsoft Copilot for Security Partner Private Preview, and is working with Microsoft product teams to help shape product development. Learn more in our news update.
With Copilot for Azure, Copilot for Sales, Copilot for Service, Microsoft Copilot Studio, and Microsoft Copilot for Security, Microsoft is expanding its range of AI-powered technologies to help you streamline cloud orchestration and management, boost sales productivity, improve customer service, spur innovation, and secure your data and resources. The sooner you start exploring these tools, the sooner you’ll be ready to empower your teams for even greater success.
BUI Cloud Security Architect Neil du Plessis is a certified CISSP and Microsoft Cybersecurity Expert specialising in holistic, cloud-powered defences for modern workplaces.
Wondering if Copilot for Microsoft 365 is right for your organisation? Join the BUI team for an interactive workshop and we’ll assess your Copilot for Microsoft 365 readiness and define a road map for your adoption journey. The workshop is conducted virtually, and is suitable for senior business development managers, line-of-business leaders, managers, technical decision-makers, and end-users. Register your interest by completing this digital form and we’ll contact you directly.
By Neil du Plessis | Cloud Security Architect, BUI
More than three-quarters of early users said that once they tried Copilot for Microsoft 365, they didn’t want to give it up. Why? Because having this AI-powered assistant as their workplace aide helped them to save time, unleash their creativity, enhance their skills, and unlock the full potential of their favourite Microsoft 365 apps.
In the Work Trend Index Special Report published by Microsoft last year, the same early users said that Copilot for Microsoft 365 empowered them to do more – and do it more efficiently than before. From creating presentations in PowerPoint to managing emails in Outlook, Copilot helped them achieve their goals.
But how exactly can Copilot for Microsoft 365 help you and your teams? How can you take advantage of this technology in your business right now? Let’s explore three everyday use cases for Copilot for Microsoft 365 in the modern workplace.
Whether you need to write a blog post, a newsletter, a proposal, or a summary, Copilot can help you with the creative process.
You can tell Copilot to draft an outline, a title, a hook, or a conclusion for your document based on your topic and purpose. You can get Copilot to check your grammar and spelling and edit, rewrite, or paraphrase your text to improve the tone, style, and clarity.
You can also direct Copilot to help you with formatting, referencing, and citing your sources so that your entire document is eye-catching, precise, and correctly attributed.
With Copilot as your co-creator, you can speed up the writing process and craft compelling content that meets your needs. Watch these videos for a closer look at what’s possible with Copilot in Word.
Whether you need to work with numbers, charts, tables, or graphs, Copilot can help you with data analysis and presentation.
You can get Copilot to perform calculations, apply formulas, filter data, or create pivot tables in Excel, based on your data set and goal.
You can ask Copilot to help you interpret and make sense of your data by providing summaries, trends, or insights in natural language.
You can also use Copilot to generate charts and graphs so that you can visualise your data, highlight relevant information, and vividly present your findings.
With Copilot by your side in Excel, you can enhance the way you work with and analyse data. Watch these videos to see how Copilot filters, formats, and reviews data.
Whether you need to plan a project, schedule a meeting, or follow up on an email, Copilot can help you with task management and day-to-day organisation.
You can ask Copilot to create a project plan, a timeline, or a checklist in Word, Excel, or PowerPoint, based on your project scope and deliverables.
You can instruct Copilot to schedule a meeting, send an invitation to your chosen attendees, and create an agenda to match the meeting topic – all from within Outlook or Teams.
You can also get Copilot to help you respond to emails, create tasks, and set reminders in Outlook or Teams, based on your email content and priorities.
With Copilot as your digital assistant, you can stay on top of your tasks and organise your calendar more efficiently. Watch these videos for an overview of Copilot’s functionality in Outlook and Teams.
Real-time intelligent assistance from Copilot for Microsoft 365 enables people to work more creatively and productively. More than 80% of surveyed users said Copilot makes it easier to get started on a first draft; take action after a meeting; and catch up on what they missed. More than 70% said Copilot helped them complete work faster and save time on mundane tasks. And 68% said Copilot improved the quality of their work.
Going forward, those who embrace Copilot for Microsoft 365 as an ally at work and take the time to build new digital habits will benefit the most from this powerful technology.
BUI Cloud Security Architect Neil du Plessis is a certified CISSP and Microsoft Cybersecurity Expert specialising in holistic, cloud-powered defences for modern workplaces.
Wondering if Copilot for Microsoft 365 is right for your organisation? Join the BUI team for an interactive workshop and we’ll assess your Copilot for Microsoft 365 readiness and define a road map for your adoption journey. The workshop is conducted virtually, and is suitable for senior business development managers, line-of-business leaders, managers, technical decision-makers, and end-users. Register your interest by completing this digital form and we’ll contact you directly.